Security
Threat models, control strategies, and defensive design patterns for agent systems operating in production.
Adjacent tracks
AI Model Watermarking for Enterprise Security
How cryptographic and forensic watermarks embedded in AI models and outputs help enterprises prove ownership, detect misuse, and meet compliance.
How to Analyze Multi-Agent AI Attack Surfaces
Framework to inventory agents, map dependencies, detect context poisoning and prompt injection, and apply behavioral and static analysis to secure multi-agent AI.
MAESTRO Framework: Threat Modeling for AI Agents
MAESTRO maps AI agent security into seven layers to identify and mitigate adversarial attacks, data poisoning, impersonation, and runtime threats.

Top Features of AI Vulnerability Scanning Tools
Key features of AI vulnerability scanners: real-time monitoring, AI-specific threat detection, CI/CD and MLOps integration, governance and scalable fixes.
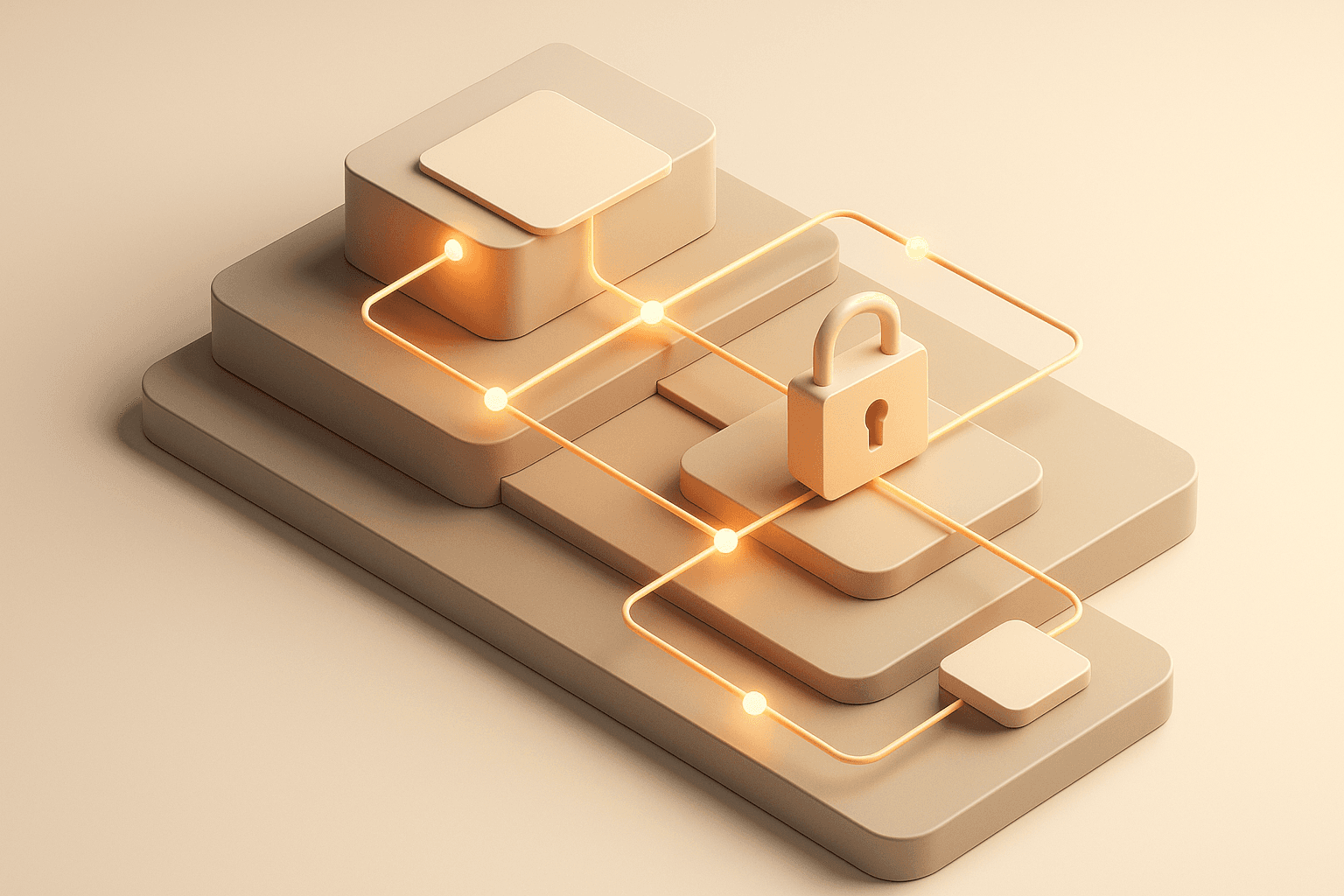
How to Monitor Access Control in AI Pipelines
Use identity-based RBAC, continuous logging, dashboards, CI/CD policy-as-code, and testing to detect and respond to access issues in AI pipelines.
Solving AI Agent Scalability Issues
Explore effective strategies for managing the identity lifecycle of AI agents, ensuring security, compliance, and scalability in dynamic environments.
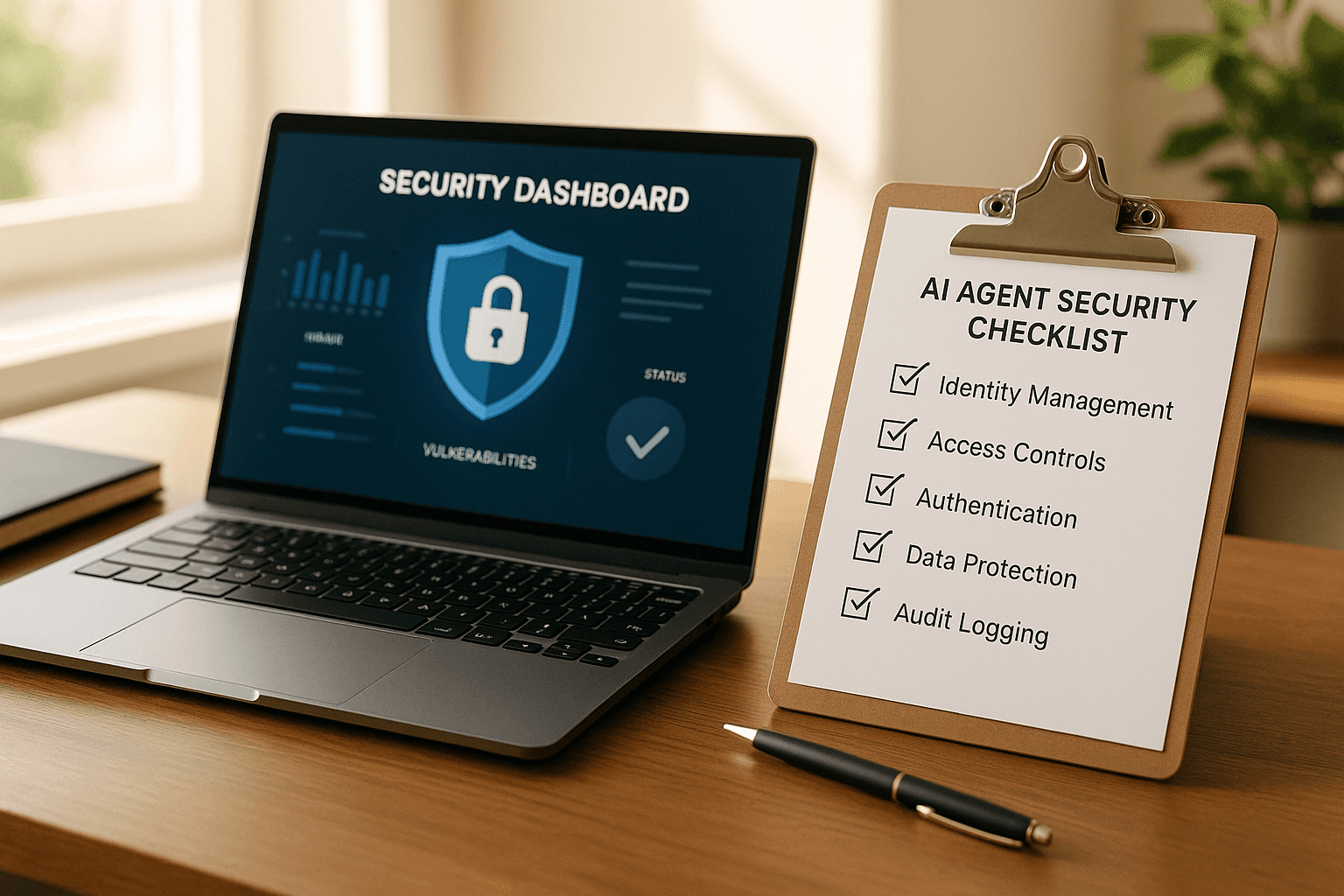
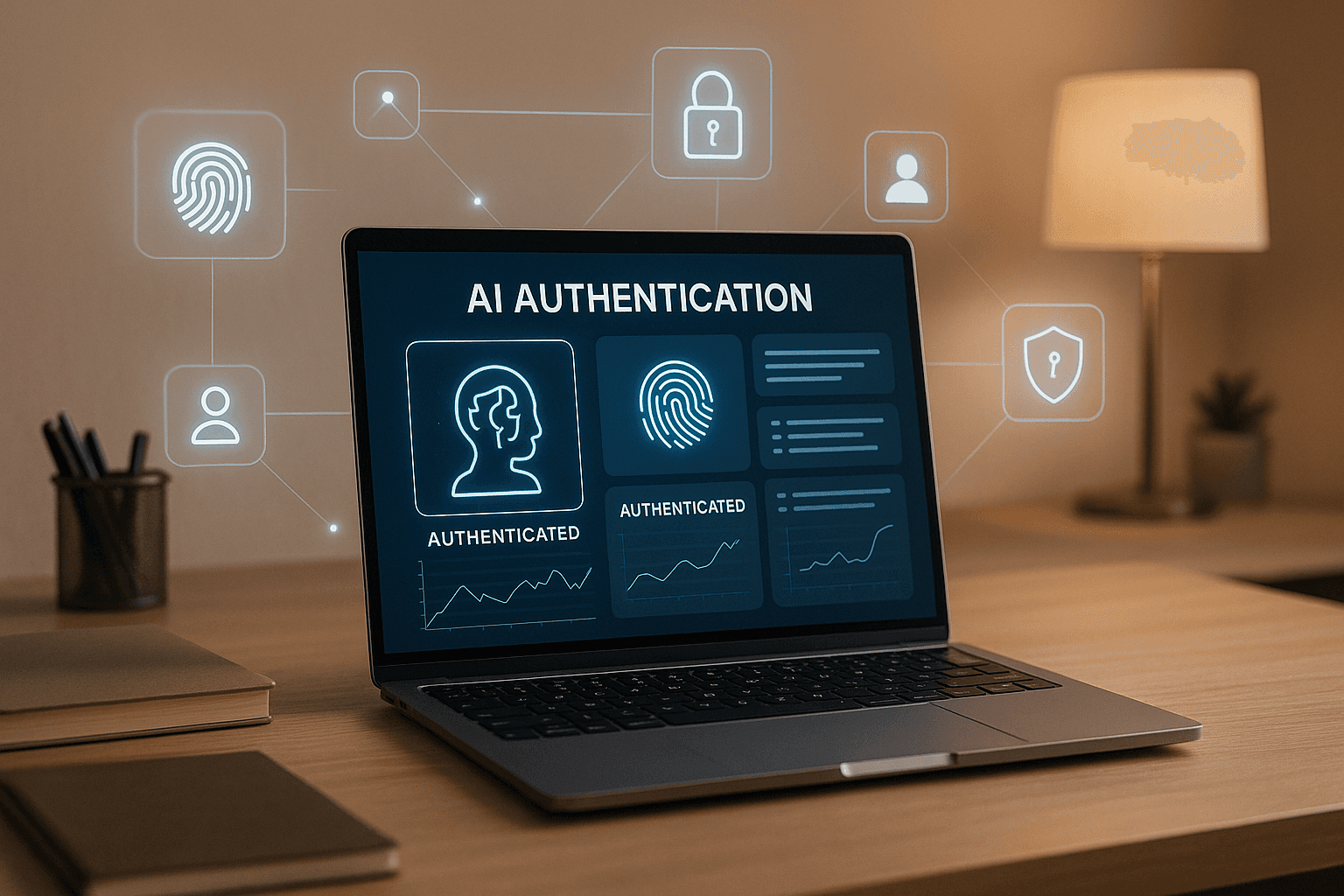
AI Agent Security Checklist for CTOs
Explore essential security strategies for AI agents, focusing on identity management, authentication, risk controls, and compliance.

Beyond the Prompt: Securing Agent Behavior, Not Just Access
Securing agent behaviour
Security Risks in the Age of Autonomous Agents: Beyond Traditional Secrets Management
Beyond secrets management

Zero Trust for Agents: What It Actually Looks Like
Zero Trust for Agents
How to Secure Agents Acting on Behalf of Users
Securing agents acting as humans

The Modern Fortress: User Management as Strategic Defense
Prefactor's view on the future of Authentication, Authorization and Audit