MCP
Model Context Protocol architecture, security patterns, implementation details, and enterprise readiness for MCP deployments.
Adjacent tracks
Best Practices for MCP Audit Compliance
Secure MCP agent access with least-privilege controls, tamper-proof audit trails, automated access reviews, real-time monitoring, and permission fixes.
MCP Breach Detection Best Practices
Secure MCP systems with detailed logging, EDR and AI behavioral analytics, protocol validation, centralized audit trails, and rapid containment controls.
Best CI/CD Tools for MCP Integration
Compare GitHub Actions, GitLab CI, Azure DevOps, Jenkins, and cloud-native CI for secure MCP integration and agent governance with Prefactor.
MCP MFA Compliance Checklist
Practical checklist to enforce phishing-resistant MFA, secure AI agent identities, apply RBAC, and log/audit MCP access for regulatory compliance.
How MCP Secures Agent Authentication
How MCP leverages OAuth 2.1, OpenID Connect, PKCE, and resource indicators to delegate identity, enforce least-privilege, and audit agent actions.
How MCP Secures Agent Authentication Compliance
How MCP uses OAuth 2.1 with PKCE, resource indicators, scoped tokens, and audit trails to enforce least privilege and meet regulatory requirements.
MCP Security: Dynamic Authorization Explained
How MCP uses OAuth 2.1, resource indicators, and short-lived scoped tokens to give AI agents fine-grained, auditable access while supporting compliance.
How MCP Secures Human-to-Agent Delegation
Tie AI agent actions to verified users with scoped, short-lived tokens, audit trails, and HITL approvals to prevent over-permissioning and token misuse.

MCP Security for Multi-Tenant AI Agents: Explained
Secure multi-tenant AI agents with MCP using tenant-specific IDs, short-lived tokens, encryption, and audit trails; covers isolation, auth, and governance.
How MCP Enhances Audit Trails for Agent Authentication
How MCP gives AI agents unique identities and uses OAuth 2.1+PKCE while Prefactor adds real-time, context-rich audit trails for compliance.
Real-Time Agent Logging with MCP
Structured JSON logs, correlation IDs, and Prefactor audit trails for secure, real-time agent monitoring, debugging, and compliance.
How MCP Enhances AI Agent Security in Multi-Cloud
Standardize AI agent identity, scoped tokens, and real-time policy enforcement across AWS, Azure, and GCP; Prefactor automates token workflows and audit trails.
How MCP Secures Agent Identity Lifecycle
Secure AI agent identities with MCP and Prefactor using OAuth/OIDC, scoped provisioning, automated credential rotation, continuous monitoring, and instant revocation.
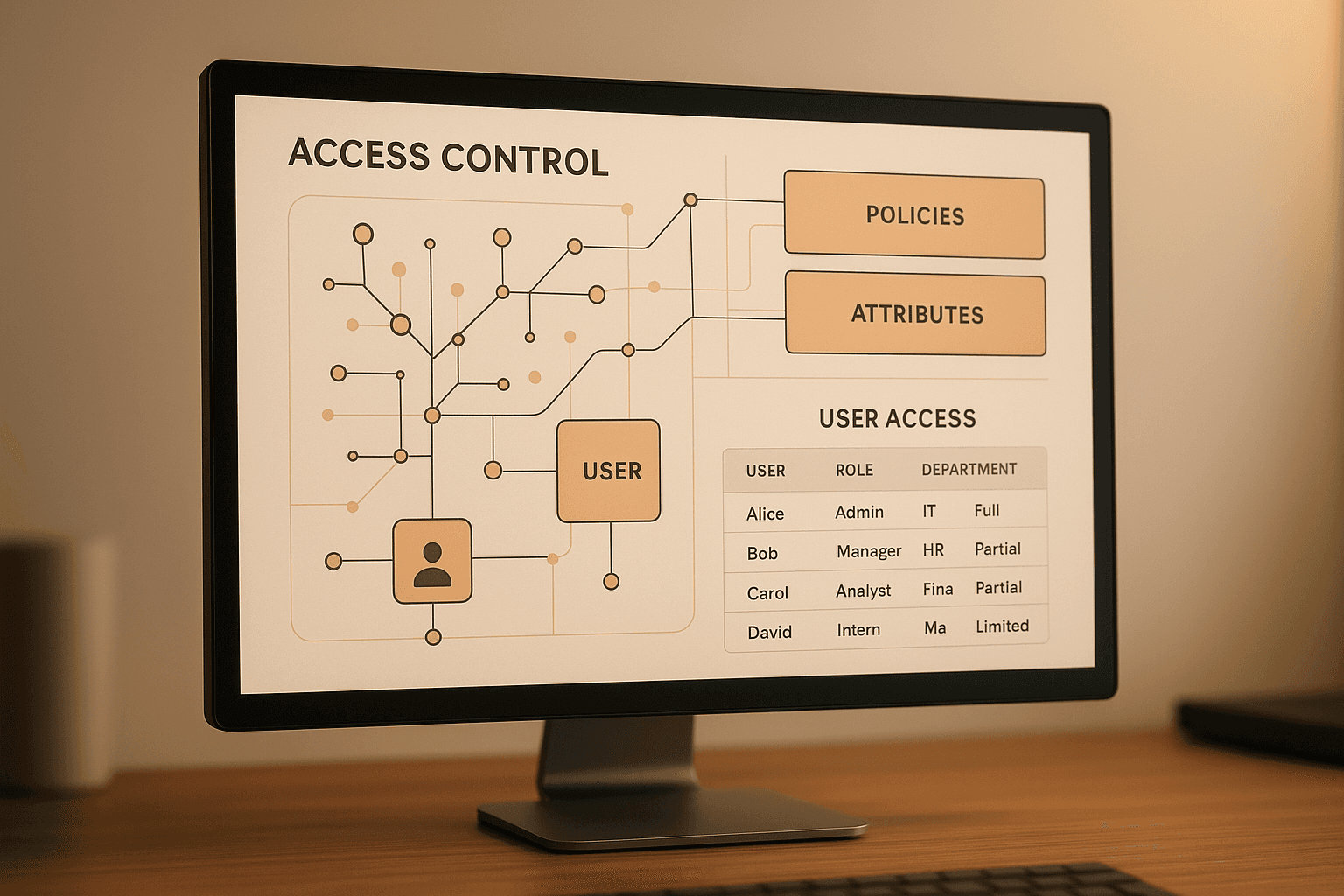
Ultimate Guide to ABAC for MCP Authentication
ABAC for AI agents in MCPs: attribute models, policy engines, default-deny enforcement, resource-root controls, testing, and audit trails for precise, scalable access control.
Granular Access Control with MCP
How MCP uses OAuth 2.1, scoped tokens, and policy-as-code to enforce least-privilege access for AI agents, multi-tenant apps, and CI/CD workflows.

How to Secure MCP Servers with OAuth 2.1 in FastAPI
Learn how to implement OAuth 2.1 authentication for MCP servers in FastAPI. Step-by-step guide for securing remote AI applications.

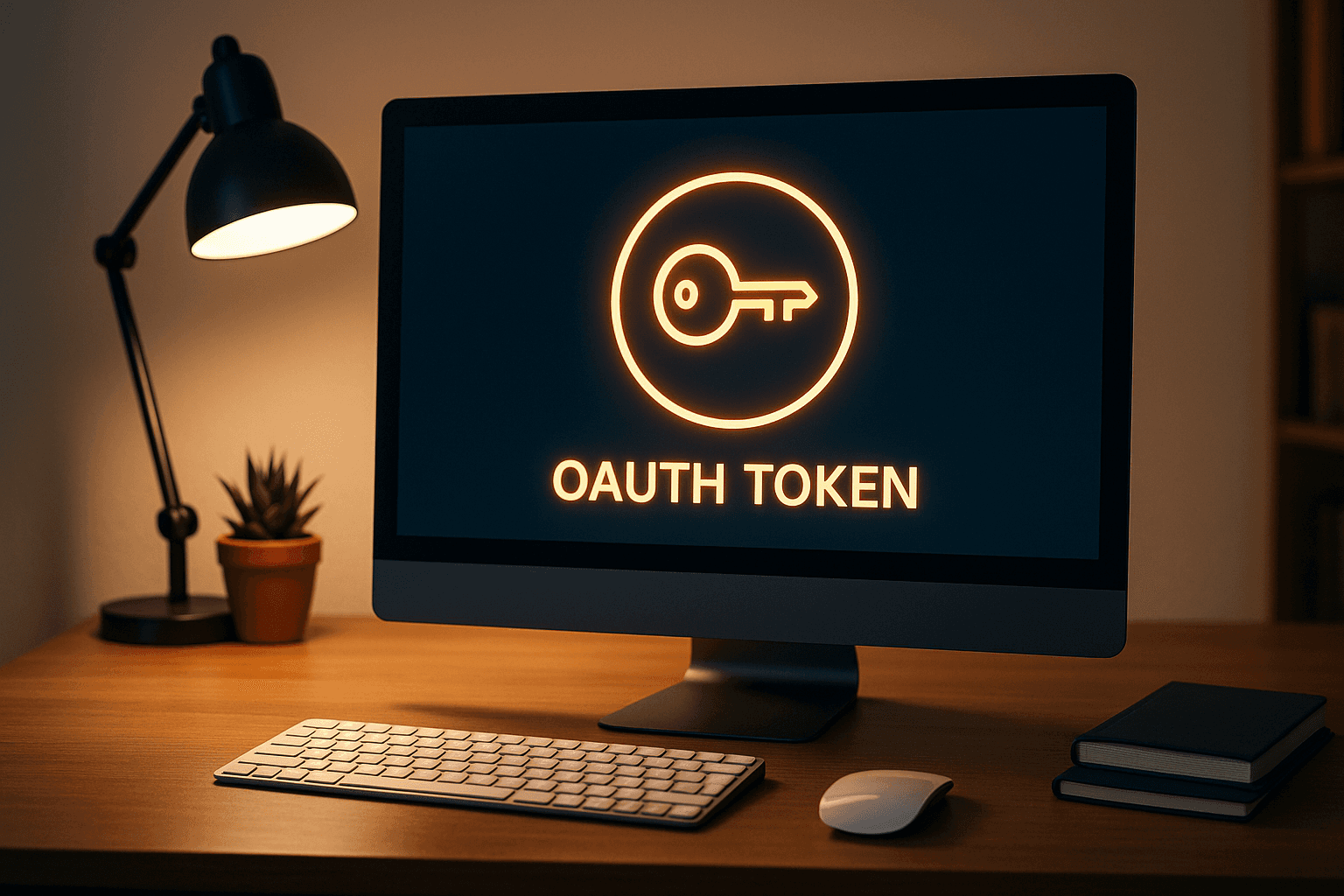
Complete Guide to MCP OAuth Authentication
Learn MCP OAuth authentication and authorization with practical steps, examples, and key concepts for secure client-server communication.
Model Context Protocol: Setup and Implementation
Learn how to implement the Model Context Protocol for secure, automated authentication between AI agents and systems, enhancing compliance and efficiency.
10 MCP Authentication Requirements Your Current Provider Probably Doesn't Support
Discover 10 critical MCP authentication features traditional providers don't support: DCR, agent-to-agent flows, transparent token exchange, and machine-scale performance.
Should I Use My Auth Provider for MCP (and Agents)?
Discover why traditional auth providers fail for MCP and AI agents. Learn about DCR, autonomous agents, and MCP-to-MCP communication. Prefactor offers the only purpose-built authentication solution for AI agent ecosystems.
How to Build a Security-First MCP Architecture: Design Patterns and Implementation
Architectural patterns for building inherently secure MCP systems, including zero-trust principles, defense in depth, and secure by design approaches for AI agents.
Why Traditional API Security Fails with MCP and What to Do Instead
Analysis of why conventional API security approaches don't work for MCP, and new security paradigms needed for AI agent architectures and autonomous systems.
How to Secure Third-Party MCP Integrations: Atlassian, Linear, and Canva
Security framework for popular MCP integrations including Atlassian MCP, Linear MCP, and Canva MCP, covering API security and data protection strategies.

What Security Controls Should You Implement for Enterprise MCP Deployments?
Enterprise-grade security checklist covering network security, data governance, compliance requirements, and audit trails for large-scale MCP deployments.
How to Secure Claude Code MCP Integrations in Production
How to secure Claude Code MCP integrations in production with scoped access, runtime controls, and auditable tool permissions.
Where MCP Security Breaks: Common Attack Vectors and Prevention
Analysis of common MCP attack patterns including prompt injection, privilege escalation, and data poisoning, with prevention strategies.
Why MCP Inspector is Essential for Security Testing and Validation
Deep dive into using MCP Inspector for security testing, vulnerability discovery, and protocol validation, with practical testing scenarios.
How to Implement MCP Authorization: A Complete Security Guide
Step-by-step guide to implementing robust authorization for MCP servers, covering OAuth, API keys, role-based access control, and delegation patterns

What Are the Critical MCP Security Risks Every Developer Must Know?
Model Context Protocol (MCP) introduces unique security challenges that traditional API security doesn't address.
MCP vs AI Agents: What’s the Difference?
Learn the difference between Model Context Protocol (MCP) and AI agents — and how MCP provides the access and security layer that agents need to function safely.
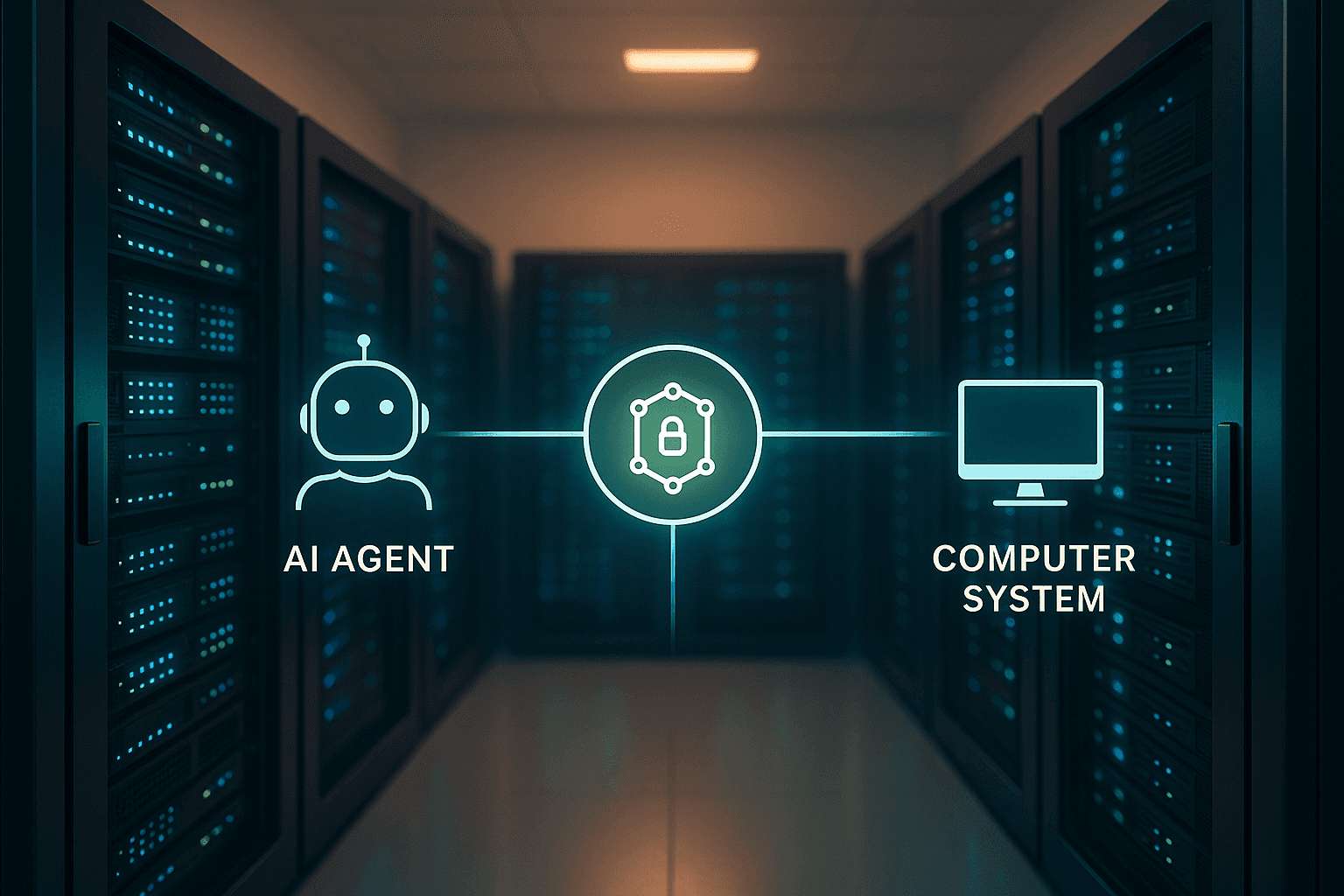
How Is MCP Auth Different from Human Auth?
Understand the core differences between Model Context Protocol(MCP) authentication and traditional human authentication, and why agent-first systems need new access models.
How Does MCP Handle Authentication?
Explore how Model Context Protocol (MCP) authenticates agents, validates delegation, and secures machine-to-machine communication.
What Is an MCP Gateway?
Learn what an MCP Gateway is, how it fits into the Model Context Protocol stack, and how it simplifies secure agent access to APIs.
What’s the Difference Between an MCP Server and MCP Client?
Understand the difference between MCP servers and MCP clients — and how they work together to enable secure access for AI agents and automated systems.

Top 10 MCP Security Risks (and How to Avoid Them)
MCP (Model Context Protocol) opens the door to powerful agentic AI — but also introduces serious security risks. Here are the top 10 vulnerabilities in MCP deployments, and how your team can defend against them.
What Is MCP — and Why Is Everyone Talking About It?
Learn what Model Context Protocol (MCP) is, why it's suddenly everywhere, and what it means for the future of AI agents, APIs, and secure access.
MCP vs LLM: What’s the Difference?
Understand the difference between Model Context Protocol (MCP) and Large Language Models (LLMs) — and how they interact in AI-powered systems.
What’s the Difference Between MCP and an API?
Understand how Model Context Protocol (MCP) differs from traditional APIs — and why it matters for agent-based access, identity, and control.
Does MCP Support OAuth? How They Work Together
Learn what Model Context Protocol(MCP) is, why it's suddenly everywhere, and what it means for the future of AI agents, APIs, and secure access.
How to Implement MCP Authentication (Step-by-Step Guide for SaaS apps)
Learn how to implement MCP authentication for AI agents using scoped delegation, agent identity, and signed access tokens. This guide covers token generation, validation, and best practices for MCP login support in SaaS and AI-native apps.