
Matt Doughty
Matt Doughty is Co-founder and CEO of Prefactor. He writes about AI agent governance, runtime controls, and the controls enterprise teams need to deploy agents safely.
5 Questions Every Head of AI Should Ask About Agent Governance
Scaling AI agents from pilots to production requires governance infrastructure. These five questions help Heads of AI evaluate whether their organisation can scale agents responsibly.
5 Questions Every ML Engineer Should Ask About Agent Runtime Controls
ML engineers building AI agents need runtime controls that work with their development workflow — not against it. These five questions help evaluate agent governance from an engineering perspective.
5 Questions Every AI Product Manager Should Ask About Agent Governance
AI product managers must balance user experience with governance requirements. These five questions help PMs ship agent-powered products that are both useful and responsible.
5 Questions Every Risk Manager Should Ask About AI Agent Deployments
AI agents introduce risk categories that traditional risk frameworks do not cover. These five questions help risk managers evaluate and mitigate the unique risks of autonomous AI agents.
5 Questions Every CISO Should Ask Before Deploying AI Agents
AI agents introduce attack surfaces that traditional security tools were not designed for. These five questions help CISOs evaluate whether their organisation is ready to deploy agents safely.
5 Questions Every AI Governance Lead Should Ask About Agent Oversight
AI governance frameworks designed for models do not cover agents. These five questions help governance leads extend their programmes to address the unique challenges of autonomous AI agents.
Taming the Lobster: Announcing Prefactor’s Integration with OpenClaw
Prefactor announces a new integration with OpenClaw (Clawdbot)
AI Model Watermarking for Enterprise Security
How cryptographic and forensic watermarks embedded in AI models and outputs help enterprises prove ownership, detect misuse, and meet compliance.
How to Analyze Multi-Agent AI Attack Surfaces
Framework to inventory agents, map dependencies, detect context poisoning and prompt injection, and apply behavioral and static analysis to secure multi-agent AI.
Best Practices for MCP Audit Compliance
Secure MCP agent access with least-privilege controls, tamper-proof audit trails, automated access reviews, real-time monitoring, and permission fixes.
AI Agent Identity Audits: Reporting Standards
Standards for auditing AI agent identities, metrics, and reports to ensure traceability, verified human ownership, and compliance with HIPAA, SOX, and GDPR.
MCP Breach Detection Best Practices
Secure MCP systems with detailed logging, EDR and AI behavioral analytics, protocol validation, centralized audit trails, and rapid containment controls.
Best CI/CD Tools for MCP Integration
Compare GitHub Actions, GitLab CI, Azure DevOps, Jenkins, and cloud-native CI for secure MCP integration and agent governance with Prefactor.
MAESTRO Framework: Threat Modeling for AI Agents
MAESTRO maps AI agent security into seven layers to identify and mitigate adversarial attacks, data poisoning, impersonation, and runtime threats.
MCP MFA Compliance Checklist
Practical checklist to enforce phishing-resistant MFA, secure AI agent identities, apply RBAC, and log/audit MCP access for regulatory compliance.
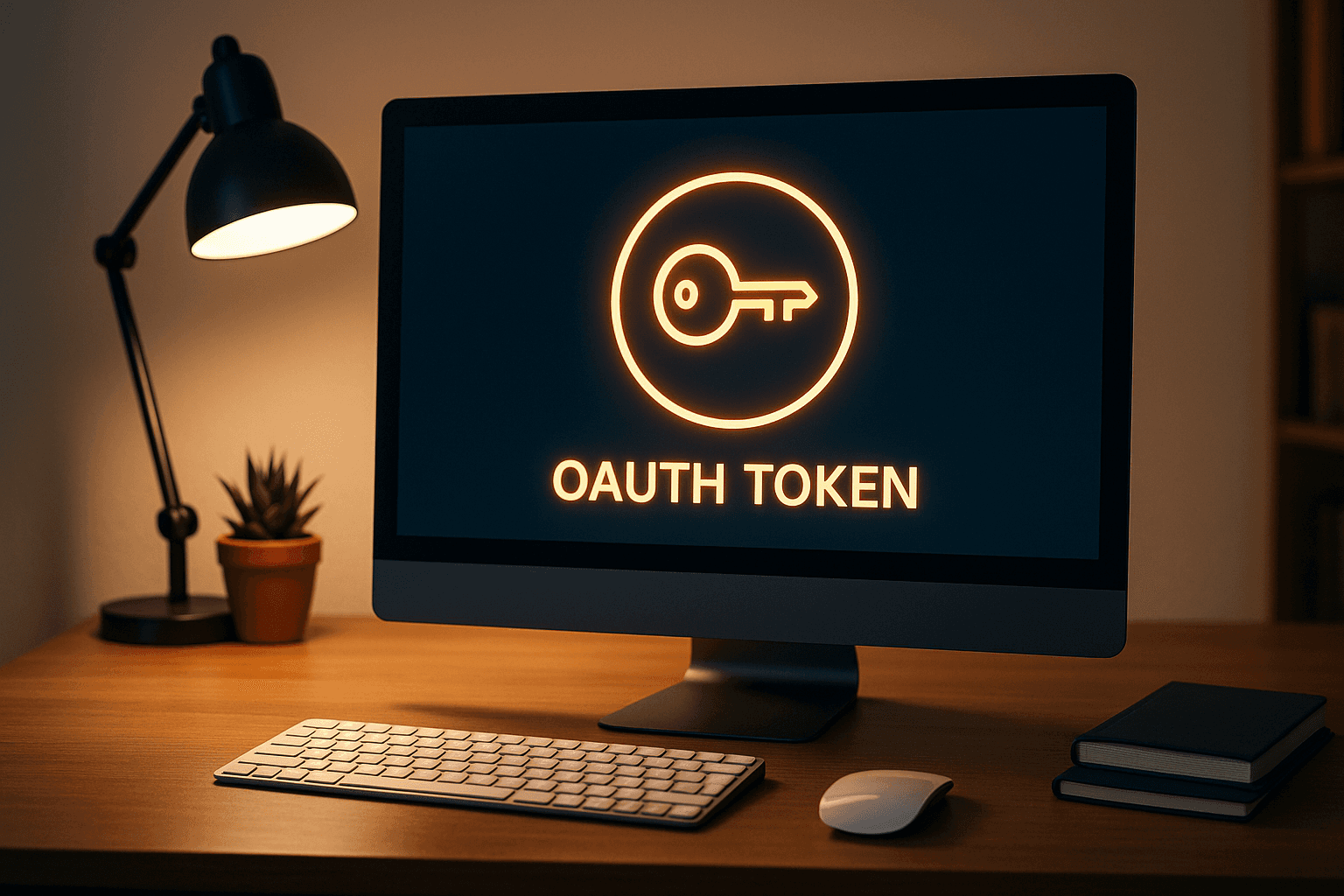
How MCP Secures Agent Authentication
How MCP leverages OAuth 2.1, OpenID Connect, PKCE, and resource indicators to delegate identity, enforce least-privilege, and audit agent actions.

Top Features of AI Vulnerability Scanning Tools
Key features of AI vulnerability scanners: real-time monitoring, AI-specific threat detection, CI/CD and MLOps integration, governance and scalable fixes.
How MCP Secures Agent Authentication Compliance
How MCP uses OAuth 2.1 with PKCE, resource indicators, scoped tokens, and audit trails to enforce least privilege and meet regulatory requirements.
Data Retention for AI Agents in Regulated Industries
Guidance on AI agent log retention across healthcare, finance, and EU/US law—recommended retention periods, privacy controls, and centralized compliance practices.
How to Monitor Access Control in AI Pipelines
Use identity-based RBAC, continuous logging, dashboards, CI/CD policy-as-code, and testing to detect and respond to access issues in AI pipelines.
Best Practices for Agent-to-Agent Authentication
Secure AI agent interactions with unique identities, short-lived tokens, mTLS, OAuth client credentials, and continuous monitoring for audit and compliance.
Audit Trails in CI/CD: Best Practices for AI Agents
Checklist to build immutable, centralized audit trails in CI/CD that trace AI agent actions, ensure regulatory compliance, and speed incident response.
Securing AI Agents with Role-Based Delegation
Secure AI agents with scoped, short-lived roles and RFC 8693 delegation tokens, enforcing least privilege, RBAC+ABAC, audit trails, and centralized governance for compliance.
MCP Security: Dynamic Authorization Explained
How MCP uses OAuth 2.1, resource indicators, and short-lived scoped tokens to give AI agents fine-grained, auditable access while supporting compliance.
How MCP Secures Human-to-Agent Delegation
Tie AI agent actions to verified users with scoped, short-lived tokens, audit trails, and HITL approvals to prevent over-permissioning and token misuse.

MCP Security for Multi-Tenant AI Agents: Explained
Secure multi-tenant AI agents with MCP using tenant-specific IDs, short-lived tokens, encryption, and audit trails; covers isolation, auth, and governance.
How MCP Enhances Audit Trails for Agent Authentication
How MCP gives AI agents unique identities and uses OAuth 2.1+PKCE while Prefactor adds real-time, context-rich audit trails for compliance.
Ultimate Guide to Non-Human Identity Risk Mitigation
How to inventory, secure, rotate, and monitor machine identities—API keys, service accounts, and AI agents—to enforce least privilege and reduce breach risk.
PKCE in OAuth for AI Agents: Best Practices
Guide to PKCE for AI agents: generate S256 verifiers, enforce PKCE server-side, use short scoped tokens, validate redirects, and monitor PKCE flows.
Regulatory Standards for AI Agent Identity
Assign cryptographic identities to AI agents, enforce time-limited least-privilege access, and maintain auditable logs to meet GDPR, HIPAA, and NIST requirements.
Real-Time Agent Logging with MCP
Structured JSON logs, correlation IDs, and Prefactor audit trails for secure, real-time agent monitoring, debugging, and compliance.
How MCP Enhances AI Agent Security in Multi-Cloud
Standardize AI agent identity, scoped tokens, and real-time policy enforcement across AWS, Azure, and GCP; Prefactor automates token workflows and audit trails.
How MCP Secures Agent Identity Lifecycle
Secure AI agent identities with MCP and Prefactor using OAuth/OIDC, scoped provisioning, automated credential rotation, continuous monitoring, and instant revocation.
How Scoped Authorization Secures AI Agents
Scoped OAuth/OIDC tokens give AI agents least-privilege, context-aware access with short lifetimes, audit trails, and revocable just-in-time credentials.
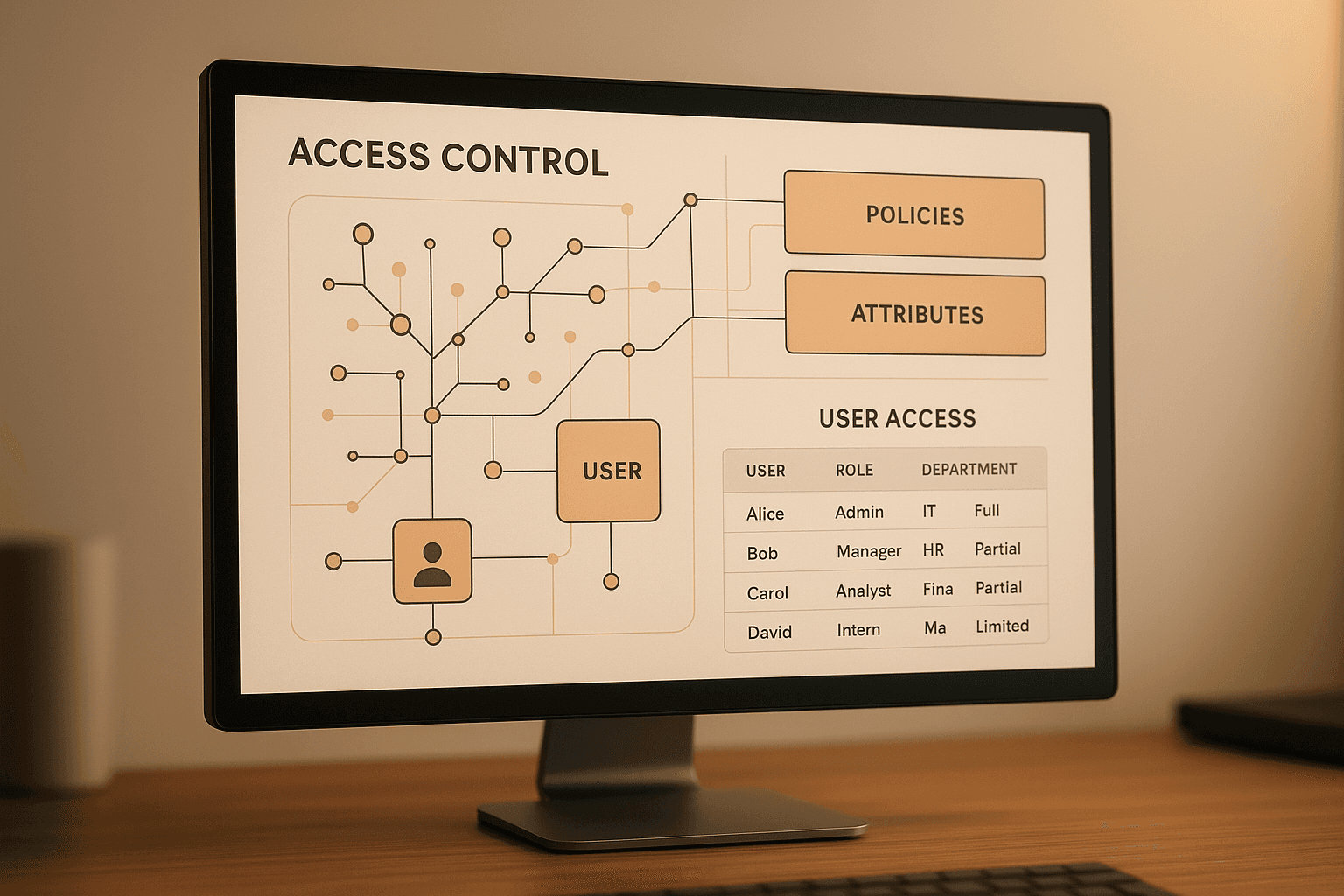
Ultimate Guide to ABAC for MCP Authentication
ABAC for AI agents in MCPs: attribute models, policy engines, default-deny enforcement, resource-root controls, testing, and audit trails for precise, scalable access control.

AI Agent Identity Lifecycle: Best Practices
Treat AI agents as first-class identities: enforce least-privilege provisioning, short-lived tokens, CI/CD automation, continuous monitoring, and secure deprovisioning.
Granular Access Control with MCP
How MCP uses OAuth 2.1, scoped tokens, and policy-as-code to enforce least-privilege access for AI agents, multi-tenant apps, and CI/CD workflows.
Deploy Phishing-Resistant Passkeys: A Practical Guide
Discover how phishing-resistant passkeys and physical security keys enhance enterprise authentication, reducing breaches and improving security.
CI/CD Integration for AI Agents: Q&A
Explore the complexities and security challenges of integrating AI agents into CI/CD pipelines, along with best practices for effective management.
Ultimate Guide to Multi-Tenant AI Systems
Explore the complexities of multi-tenant AI systems, focusing on security, identity management, and compliance challenges.

How to Secure MCP Servers with OAuth 2.1 in FastAPI
Learn how to implement OAuth 2.1 authentication for MCP servers in FastAPI. Step-by-step guide for securing remote AI applications.

Complete Guide to MCP OAuth Authentication
Learn MCP OAuth authentication and authorization with practical steps, examples, and key concepts for secure client-server communication.

Delegated Access vs Direct Access: Which to Choose
Explore the differences between Delegated Access and Direct Access for AI agents, focusing on security, efficiency, and compliance considerations.
Model Context Protocol: Setup and Implementation
Learn how to implement the Model Context Protocol for secure, automated authentication between AI agents and systems, enhancing compliance and efficiency.
Solving AI Agent Scalability Issues
Explore effective strategies for managing the identity lifecycle of AI agents, ensuring security, compliance, and scalability in dynamic environments.
Top 7 AI Agent Authentication Platforms in 2026
Comparing the best AI agent authentication platforms in 2026: Prefactor, Runlayer, Composio, Okta, and more. Find the right fit for your agent security stack.
AI Agent Security Checklist for CTOs
Explore essential security strategies for AI agents, focusing on identity management, authentication, risk controls, and compliance.
How to Secure AI Agent Authentication in 2025
Explore essential strategies for securing AI agent authentication in 2025, focusing on unique credentials, JIT access, and compliance standards.

OAuth vs OIDC for AI Systems: Complete Guide
Explore how OAuth and OIDC secure AI systems, detailing their differences, workflows, and best practices for effective implementation.

5 Best Practices for AI Agent Access Control
Explore essential practices for securing AI agents, focusing on identity management, access control, and the importance of human oversight.
Auth0 vs Okta vs Prefactor: Which Handles AI Agent Authentication Best?
Compare Auth0, Okta, and Prefactor for AI agent authentication. See feature matrices, performance comparisons, and real implementation examples.
10 MCP Authentication Requirements Your Current Provider Probably Doesn't Support
Discover 10 critical MCP authentication features traditional providers don't support: DCR, agent-to-agent flows, transparent token exchange, and machine-scale performance.

9 AI Agent Authentication Horror Stories (And How Prefactor Prevents Them)
Real disasters from forcing AI agents into human-centric auth: $15M compliance failures, security breaches, performance meltdowns, and scaling walls.

5 Signs Your Auth Provider Can't Handle AI Agents (And What to Do About It)
Identify warning signs your auth provider wasn't built for AI agents: manual registration, false security alerts, session timeouts, and missing agent features
7 Authentication Problems You'll Hit When Deploying AI Agents at Scale
Discover the 7 authentication problems that break AI agent scaling: manual registration bottlenecks, session timeouts, rate limiting, audit trail confusion, and more.
How to Build Custom Consent Screens for AI Agents Handling Sensitive Data
Learn how to build sophisticated consent screens that explain AI agent actions clearly. Discover advanced authorization patterns beyond basic authentication
How to Add AI Agent Authentication Without Replacing Your Existing Auth Provider
Don't replace your existing auth provider. Learn how Prefactor wraps around Auth0, Okta, or Azure AD to add AI agent capabilities without migration.
How to Let AI Agents Access Google and Microsoft APIs Without Multiple OAuth Flows
Learn how transparent token exchange lets users authenticate once with Google/Microsoft while AI agents get seamless API access without multiple OAuth flows.
How to Manage Authentication Sessions for 24/7 AI Agents vs Human Users
Discover why 24/7 AI agents need different session management than human users. Learn how Prefactor's labeled agent sessions prevent timeouts and monitoring noise.

How to Handle Dynamic Client Registration for AI Agents That Spawn and Terminate Automatically
Learn why AI agents need device-like Dynamic Client Registration, not application-style permanent registration. Discover how Prefactor's DCR handles ephemeral agent lifecycles automatically.
Should I Use My Auth Provider for MCP (and Agents)?
Discover why traditional auth providers fail for MCP and AI agents. Learn about DCR, autonomous agents, and MCP-to-MCP communication. Prefactor offers the only purpose-built authentication solution for AI agent ecosystems.
How to Build a Security-First MCP Architecture: Design Patterns and Implementation
Architectural patterns for building inherently secure MCP systems, including zero-trust principles, defense in depth, and secure by design approaches for AI agents.
Why Traditional API Security Fails with MCP and What to Do Instead
Analysis of why conventional API security approaches don't work for MCP, and new security paradigms needed for AI agent architectures and autonomous systems.
How to Secure Third-Party MCP Integrations: Atlassian, Linear, and Canva
Security framework for popular MCP integrations including Atlassian MCP, Linear MCP, and Canva MCP, covering API security and data protection strategies.

What Security Controls Should You Implement for Enterprise MCP Deployments?
Enterprise-grade security checklist covering network security, data governance, compliance requirements, and audit trails for large-scale MCP deployments.
How to Secure Claude Code MCP Integrations in Production
How to secure Claude Code MCP integrations in production with scoped access, runtime controls, and auditable tool permissions.
Where MCP Security Breaks: Common Attack Vectors and Prevention
Analysis of common MCP attack patterns including prompt injection, privilege escalation, and data poisoning, with prevention strategies.
Why MCP Inspector is Essential for Security Testing and Validation
Deep dive into using MCP Inspector for security testing, vulnerability discovery, and protocol validation, with practical testing scenarios.
How to Implement MCP Authorization: A Complete Security Guide
Step-by-step guide to implementing robust authorization for MCP servers, covering OAuth, API keys, role-based access control, and delegation patterns

What Are the Critical MCP Security Risks Every Developer Must Know?
Model Context Protocol (MCP) introduces unique security challenges that traditional API security doesn't address.
Claude x Canva Remote MCP server demo
Live demo showing how to connect Cursor to Canva using Remote MCP — enabling secure agent access across tools.
Prefactor x Claude Remote MCP server demo
Live demo showing how to connect Cursor to Canva using Remote Model Context Protocol (MCP) — enabling secure, agent-driven access between tools.
MCP vs AI Agents: What’s the Difference?
Learn the difference between Model Context Protocol (MCP) and AI agents — and how MCP provides the access and security layer that agents need to function safely.
How Is MCP Auth Different from Human Auth?
Understand the core differences between Model Context Protocol(MCP) authentication and traditional human authentication, and why agent-first systems need new access models.
How Does MCP Handle Authentication?
Explore how Model Context Protocol (MCP) authenticates agents, validates delegation, and secures machine-to-machine communication.
What Is an MCP Gateway?
Learn what an MCP Gateway is, how it fits into the Model Context Protocol stack, and how it simplifies secure agent access to APIs.
What’s the Difference Between an MCP Server and MCP Client?
Understand the difference between MCP servers and MCP clients — and how they work together to enable secure access for AI agents and automated systems.

Top 10 MCP Security Risks (and How to Avoid Them)
MCP (Model Context Protocol) opens the door to powerful agentic AI — but also introduces serious security risks. Here are the top 10 vulnerabilities in MCP deployments, and how your team can defend against them.
What Is MCP — and Why Is Everyone Talking About It?
Learn what Model Context Protocol (MCP) is, why it's suddenly everywhere, and what it means for the future of AI agents, APIs, and secure access.
MCP vs LLM: What’s the Difference?
Understand the difference between Model Context Protocol (MCP) and Large Language Models (LLMs) — and how they interact in AI-powered systems.
What’s the Difference Between MCP and an API?
Understand how Model Context Protocol (MCP) differs from traditional APIs — and why it matters for agent-based access, identity, and control.
Does MCP Support OAuth? How They Work Together
Learn what Model Context Protocol(MCP) is, why it's suddenly everywhere, and what it means for the future of AI agents, APIs, and secure access.

Top 10 Agent Integrations to Add to Your SaaS
Ten high-value agent integrations that show where identity, delegation, and runtime control start to matter for SaaS teams.

Prefactor: MCP Auth, Agent Identity, and the Future of Authentication
Prefactor is building agent-first authentication infrastructure for AI-native platforms. Learn how we support MCP, secure agent identity, and our vision for programmable, portable access across autonomous systems.
How to Implement MCP Authentication (Step-by-Step Guide for SaaS apps)
Learn how to implement MCP authentication for AI agents using scoped delegation, agent identity, and signed access tokens. This guide covers token generation, validation, and best practices for MCP login support in SaaS and AI-native apps.

Beyond the Prompt: Securing Agent Behavior, Not Just Access
Securing agent behaviour

The Compliance Conundrum: Auditing Autonomous Agent Actions
Auditing Autonomous Agent Actions
Terraforming Access: Why Auth Needs to Be Defined in Code
Infrastructure as Code for Agential Auth
How Impersonation and Delegation Break in Today’s CIAMs for AI-Native Use Cases
Why legacy CIAM models break when AI agents act for users, and how to separate impersonation from safe delegated access.
Security Risks in the Age of Autonomous Agents: Beyond Traditional Secrets Management
Beyond secrets management

How to Design Identity for AI Agents, Not Just Humans and APIs
A practical framework for designing identity around AI agents, delegated access, and runtime accountability.
The Hidden Costs of Service Account Sprawl: When Quantity Trumps Control
Cost of service account sprawl
Why M2M Tokens Aren’t Enough for Agent-Based Systems: Beyond Static Credentials
M2M tokens aren't enough
Service Accounts Are Failing in the Age of Agent Identity
Why service accounts break down for AI agents, and what an agent-first identity model needs to support.
From Static to Dynamic: What Agent Identity Actually Looks Like
What dynamic agent identity looks like in production, from short-lived credentials to revocation and auditability.

Zero Trust for Agents: What It Actually Looks Like
Zero Trust for Agents
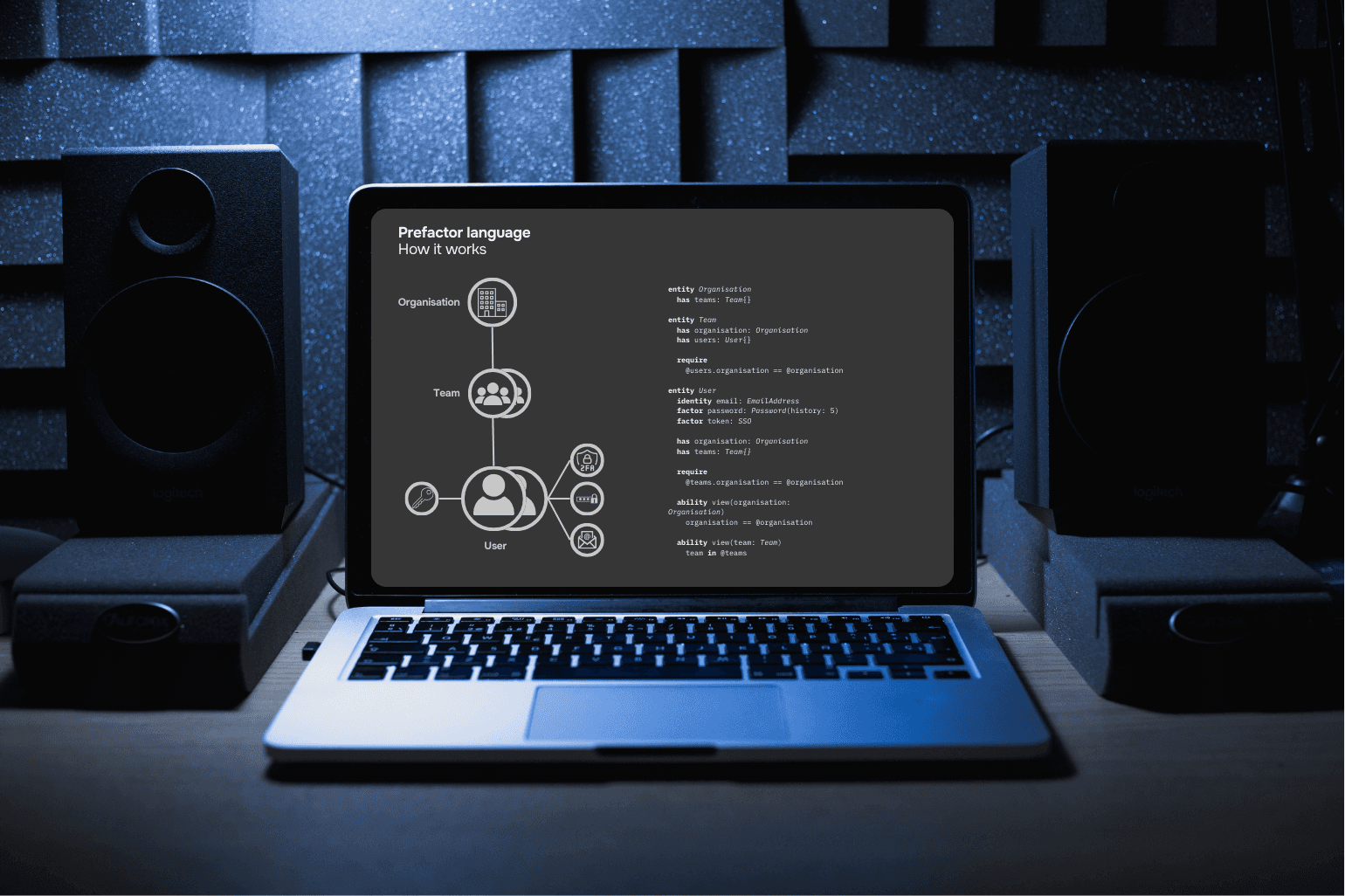
Designing a DSL for Agent Access Control
Why agent access control needs a policy language teams can version, review, and enforce across runtimes.
Impersonation ≠ Delegation: Don’t Let Agents Spoof Your Users
How to stop AI agents from spoofing user identity by enforcing explicit delegation, scoped access, and auditable actions.

Delegated Access for Agents: What Comes After Tokens
Why delegated access beats static tokens for AI agents, and what a safer handoff model looks like in production.

Agent Identity 101: Why Naming, Scoping, and Lifecycle Matter
A practical introduction to agent identity: naming, scoping, ownership, and lifecycle controls for non-human actors.

Why OAuth Alone Isn’t Enough for Agent Authentication
Why OAuth alone does not solve agent authentication, delegation, lifecycle, or runtime control.
How to Secure Agents Acting on Behalf of Users
Securing agents acting as humans

The Top 5 Problems with M2M Tokens in Agent Workflows
Top 5 problems with M2M tokens
Why Machine-to-Machine Auth Breaks in the Age of AI Agents
Why traditional machine-to-machine auth breaks for AI agents, and what a safer identity model requires.
Autonomous Agents Create a New Identity Challenge
Why autonomous agents break assumptions behind traditional identity systems, and what teams need instead.

Your Customers' AI Agents Need to Log In—Is Your SaaS Ready?
Is your saas ready for agents?
Beyond Human Login: Why Your App Needs an Agent-First Authentication Strategy
Agent First Authentication

Compare Agent Authentication Solutions
How to compare agent authentication platforms by delegation, runtime control, auditability, and developer ergonomics.
Report: Elevating API Security for Engineers: A Prefactor.tech Perspective on Modern Solutions
API Authentication Security
Build vs Buy Agent Authentication
A practical look at building versus buying authentication when AI agents need delegated access, lifecycle control, and auditability.

What Most Companies Get Wrong About Non-Human Identity Management
Common mistakes teams make with non-human identities, and what changes when AI agents become first-class actors.
How to Manage Non-Human Identities Before They Manage You
How to manage non-human identities with ownership, scoping, rotation, and lifecycle controls once AI agents enter production.
What Are Non-Human Identities in AI Agent Systems?
A clear definition of non-human identities, how they differ from service accounts and bots, and why AI agents make them harder to manage.

Authentication vs. Authorization: Understanding the Key Differences
Authentication vs authorization

Build vs Buy Authorization for AI Agents
When it makes sense to build authorization yourself, when to buy it, and what changes once AI agents need fine-grained access control.
How to Secure AI-Assisted Vibe-Coded Applications
The main risks in AI-assisted vibe-coded applications, plus practical controls for authentication, authorization, and agent safety.

How to Version and Test Your Login Flow Like Any Other Part of Your Stack
Treat your login like code — not config.

Vibe-Coding Your Startup? Here’s Why You Shouldn’t Roll Your Own Authentication
Why DIY auth breaks — and what to do instead.
Authentication Best Practices for Cursor, Windsurf, and Other AI-Coded Projects
Best practices for login flows in AI-coded apps like Cursor and Windsurf.
How to Add Login to Your Cursor AI App (Without Firebase or Auth0)
Add login to your AI-coded app with code-first auth. No Firebase. No dashboards.

Choosing the Right Authentication Solution When Coding with Cursor
Choosing authentication when vibe coding
Build vs Buy — The Real Cost of Authentication
What building authentication really costs once security, maintenance, and AI-agent support are included.
White paper: ROI of Customer Authentication platforms in 2025
ROI of a custmer authentication platform
Common Concerns About Third-Party Auth Providers
How to evaluate third-party auth providers without repeating the usual lock-in, security, and control myths.

Comparing Prefactor to Self Built
Evaluating Prefactor vs Self Built
White paper: The Future of Customer Authentication in 2025
The Future of Customer Authentication in 2025

I Built My Own Auth — How do I evaluate the right customer identity solution?
Evaluating customer identity after I've Hand rolled my own

Open or Closed: What Kind of User Identity Stack Should You Trust?
Open or Closed Source User Identity stack?

Prefactor vs Firebase for AI Agent Authentication
How Prefactor compares with Firebase for teams securing AI agents, delegated access, and non-human identities.
White paper: Build vs Buy Authentication in 2025
Build vs Buy 2025 - User management and Authentication
Why build Prefactor now?
It's a crowded space. Why now?

Our Vision for Developer Experience at Prefactor
How we're approaching developer experience in user security through our domain-specific language

Comparing Prefactor to Clerk
Evaluating Prefactor vs Clerk
Prefactor DSL: The Unified Language for Authentication, Authorization, and Audit
A powerful DSL that transforms fragmented user security into a cohesive, code-first platform for developers who need precision, control, and simplicity.

Comparing Prefactor to Kinde
Evaluating Prefactor vs Kinde
Why startups and Scale-Ups Deserve Enterprise-Grade User Management — Without the Enterprise Hassle
Unlock powerful, secure user management built for SMBs and scale-ups — no enterprise baggage required.

The Story Behind Prefactor: Built by Founders Who Lived the Problem
How Prefactor came to life direct from the founders

Prefactor vs Amazon Cognito for AI Agent Authentication
How Prefactor compares with Amazon Cognito when AI agents need delegated access, policy, and audit trails.
When Authentication and Authorization Join Forces: Why Unity Makes Sense
Why the user layer includes authentication and authorization

The Modern Fortress: User Management as Strategic Defense
Prefactor's view on the future of Authentication, Authorization and Audit